Trending Now
- Cyber Security Awareness for Students and Data Security
- Zero Trust Security: Concepts and Implementation in Campus
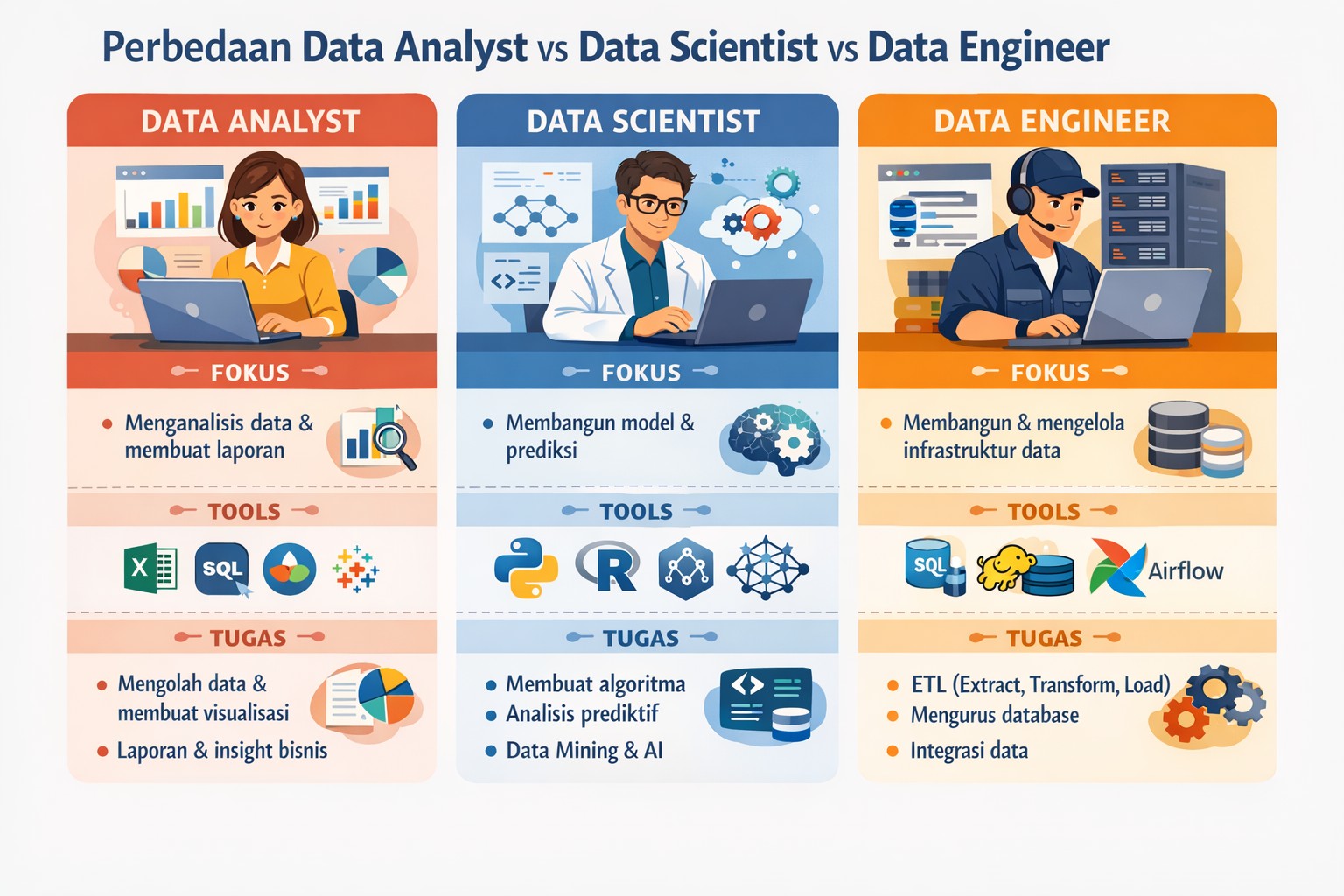
- Differences Between Data Analyst, Data Scientist, and Data Engineer
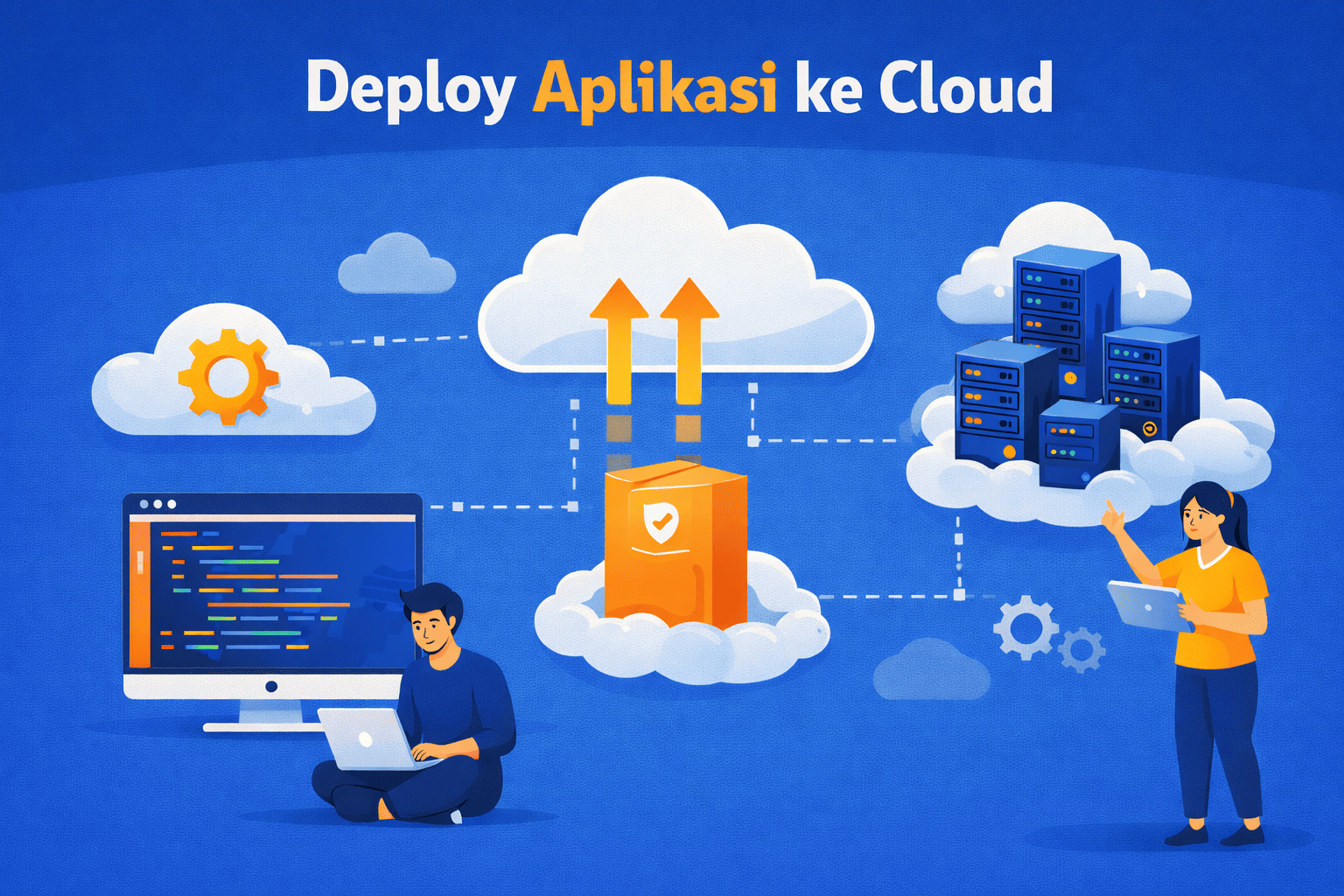
- Deploying Applications to the Cloud for Beginners Made Easy
- Differences Between DevOps and DevSecOps in System Development
- Gemini AI: Advanced Artificial Intelligence Technology
Trending News
Basically, the difference between User Interface and User Experience is quite significant. User Inte…
When performing facial recognition for an individual in your dataset, it is necessary to know the wo…
Discover the key differences between JavaScript and jQuery in our comprehensive guide. Learn how the…
Hi TelUtizen, did you know that the buildings at Telkom University have specific names? But before w…
The difference between discrete data and continuous data is very important in Data Analytics, both h…
Teknologi CRM atau Customer Relationship Management merupakan Manajemen Hubungan Pelanggan. CRM adal…
AI
Technology
Learn the definition of Big Data, its main characteristics (5V), examples of its application in ever…
What is an ISP? ISP (Internet Service Provider) is the main …
Wireless WAN, Wireless Network technology that can connect d…
SEO
Check out the 10 On Page SEO Checklist for optimization carried out on website pages with the aim of…
Technology
Four Types of Flowchart Symbols. There are many types of flo…
Learn the meaning and benefits of SWOT (Strength, Weakness, …

Blogs Direktorat PuTI
follow us
Subscribe Us
Enter your e-mail and subscribe to our newsletter. We promise not to spam.
Latest Posts
Recent Posts
Blog

BANDUNG, Telkom University – Hi TelUtizen, do you know that health s…

The managerial of a business usually applies one or both elements of Business Analytics and Bus…

What is a Web Server (Apache, Nginx, Tomcat, IIS, Jetty) and Its Relation to Websites?
A web s…

OSI Layer 2, commonly referred to as the Data Link Layer, is an essential part of the OSI (Open…

To understand accounting properly, you need to know the accounting cycle. The financing cy…

Understanding Sprint Time in the Scrum Method
The Scrum method is one of the methodologies inc…
Action
Telkom University has a counseling service that is managed by the Directorate of Student Affair…
BANDUNG, Telkom University – Hi TelUtizen, do you know that health s…
BANDUNG, Telkom University – Hi TelUtizen, do you know that health s…
BANDUNG, TEL-U – Hi Telutizens, do you know that Telkom University has a Health Card…
BANDUNG, TEL-U – Telkom University continues to evaluate the quality of Health …
BANDUNG, TEL-U – Telkom University is a private university that is well known in many circ…
Technology
Training on managing the website of the Acitya Popular Scientific Magazine
Procedures for crea…
Technology
One type of diagram in the unified modeling language is sequ…
What is coding? Coding is the process of writing instruction…
Adoption
BANDUNG, Telkom University – Hi TelUtizen, do you know that health servic…
Technology
All Telkom University students and employees can use an appl…
Standar WordPress di Tel-U sudah ditentukan oleh Direktorat …
Blogs
Learn the importance of cyber security awareness for students to avoid cyber threats such as ph…
Learn the concept of Zero Trust Security and its implementation in campuses to improve data, sy…
Learn the differences between Data Analysts, Data Scientists, and Data Engineers, including the…
Learn how to deploy applications to the cloud for beginners easily and practically, from prepar…
Meta Description:Learn the differences between DevOps and DevSecOps in system development, incl…
Most Viewed
Recent Comment
Gallery